Fig. 3.
From: A Design Methodology for Stealthy Parametric Trojans and Its Application to Bug Attacks
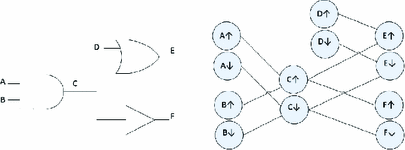
Circuit and corresponding timing graph.
From: A Design Methodology for Stealthy Parametric Trojans and Its Application to Bug Attacks
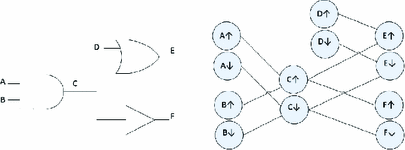
Circuit and corresponding timing graph.